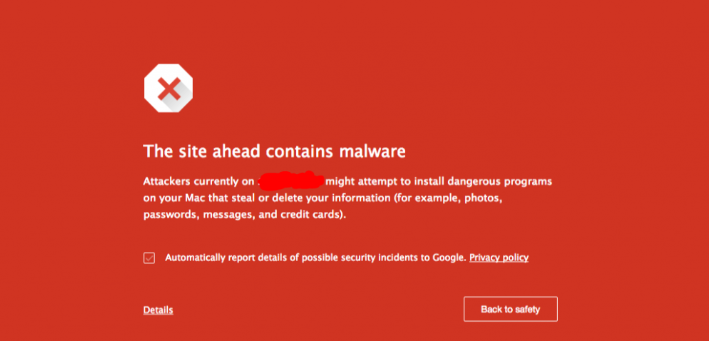
Danger of Malware – Recently, there has been a lot of incessant malware that can steal all the data on the target computer and is very dangerous because emails and various accounts that were previously entered on the computer can be taken just like that. That is one of the dangers of malware, of course from now on there is a need for a clearer understanding of malware and what the dangers are if it occurs on our computers.
Malware is not just like that, but there are various types of malware known today that can threaten your computer.
Table of Contents
What is Malware
Malware is an umbrella term for any type of malicious software designed to harm or exploit any programmable device, service, or network. Cyber criminals usually use them to extract data that they can exploit from victims for financial gain.
That data can range from financial data, to healthcare records, to personal emails and passwords, the possibilities for what type of information can be compromised are endless.
Difference between Malware, Trojan and Virus
This malware is often associated with trojans and viruses. If you look at the computer, it will have an effect like being hit by a virus or trojan, but in essence, all of this is different.
The following are the differences between malware, trojans and viruses:
Malware
Malware is an umbrella term used to cover all types of malicious software. Malware is designed to attack organizations, companies and individuals by destroying data and resources, causing errors and slowing performance. Malware can be delivered to network systems via e-mail or software installation or surfing the internet. Viruses, trojan horses, worms, and spyware are types of malware along with some of the more dangerous ones.
Trojan
Trojan Horse juga merupakan jenis malware yang menggunakan nama palsu dan palsu untuk menyesatkan pengguna dari maksud sebenarnya dan mengeksekusi mereka. Trojan Horses umumnya menginstal pada sistem sebagai perangkat lunak yang sah dan berguna yang dapat memberikan akses tidak sah dan kontrol sistem kepada peretas. Back orifice, Rootkit dan Beast Trojan adalah beberapa dari Trojan horse umum yang lebih berbahaya.
Virus
As for the virus, is a computer program or software that connects itself with other computer software or programs to damage the computer system. When a computer program runs on a virus, it performs several actions such as deleting files from the computer system. Viruses cannot be controlled remotely.
How Malware Works on Websites and Computers
Malware can spread in many ways: when you download and install infected programs, when you click infected links or open malicious email attachments, or even if you use damaged physical media such as infected USB drives.
Website
The way that can make malware spread is from websites. This is one of the openings where malware can spread very easily. Malware hazards can spread from websites in many ways, but what is very common and very, very often the cause is 3 things, namely:
Plugins
Plugins are relatively safer when you download them officially from the WordPress directory (before they appear there, they usually pass through a filter). If you download from an unofficial website, it has the potential to be inserted with malicious code (malware) of any kind (mostly adware or in the form of advertisements).
Computer Themes
Still the same as plugins, themes on websites, for example Google Chrome themes can really contain malware. This malware can once steal various data stored in browsers including users and passwords for various accounts.
Desktop Devices
When downloading software, you need to be careful because it is very possible for the application to be inserted by malware. Not infrequently the program code contains a backdoor that is used to give access rights to malware authors so they can access computer networks remotely. This will harm the affected computer devices and also other computer devices if they are connected to each other.
How to Overcome Malware
The most potent countermeasures against malware are avoiding it. Yes, the answer is certain because malware is very difficult to remove. However, there are also various applications or software that can be relied upon to be able to remove malware or at least detect malware or prevent malware from attacking computer devices or attacking websites that you manage, for example.
Antimalware
Antimalware is a type of software program created to protect information technology (IT) systems and individual computers from malicious software, or malware. Antimalware programs scan computer systems to prevent, detect, and remove malware.
Antimalware programs can help in the following ways:
- Prevent users from visiting websites known to contain malware;
- Prevent malware from spreading to other computers in the computer system;
- Provides insight into the number of infections and the time needed to eliminate them; and
- Provides insight into how malware infiltrates a device or network.
Overcoming Malware On Websites
You can try a tool called Sucuri.
The main function of this tool is to find malware or infected files on your website. The following is an example of the results of a scan of a website infected with malware using Sucuri:
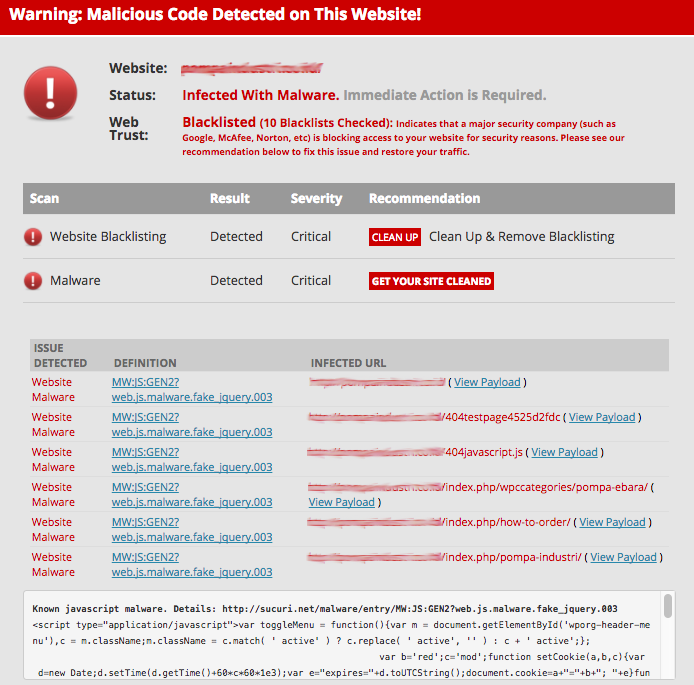
There are two options to overcome this:
- Perform a restore backup of web pages. The condition is, you have to do a backup before the site is infected. Please check with your hosting facility whether a backup file for your site really exists or not.
- Delete infected files manually. How to get rid of site malware along with this step is only temporary. We’re not suggesting you do it first.
Overcoming Malware On Computers
Sometimes the source of malware appears from the desktop device used. Because some users or users often develop websites via a local computer which are then uploaded to the website server using an FTP connection.
Before being uploaded, sometimes the malware has entered the website folder or file. After uploading malware more and more and spread. So, before uploading website files, first make sure that there is no malware in it.
There are several ways you can do to avoid Malware Hazards, namely by doing a malware scan or examining the files contained in it one by one. Look at the files one by one to make sure there are no suspicious files.
NetData is a company that provides the highest quality technology-based services. If you are interested in us, you can contact us directly via this link or via our contact form here.
![]()


