The world of information technology in Indonesia is currently busy with various international-class foreign vendors such as Sangfor. Sangfor is a multinational company based in the city of Shenzen, the city of info technology in China. The Sangfor company in China has been established since 2000 and has grown rapidly in China’s domestic market.
Not only that, currently Sangfor controls nearly 60% of the Internet Access Management market share in China and has received lots of awards like Delloite, Fortune and Frost and Sullivan. In the Gartner Magic Quadran itself, the name Sangfor has emerged in the Niche Player area since 2011.
Sangfor offers solutions that cover three areas, namely Internet Access Management, WAN Optimization, and SSL VPN. Internet Access Management is a tool that is used to add settings with a high enough efficiency level for internet access activities. This solution is needed by almost all companies considering that at this time almost all corporations have opened to the internet. With the increasing number of applications or platforms on the internet, arrangements are needed so that the use of internet access matches the company’s needs.
The WAN Optimization solution deals with increasing the performance of an application. Usually WAN Optimization is used when a user in a branch opens an application or server in the data center via a WAN network. Some of the components, including latency and bandwidth, are not large, which usually results in slow access to applications. However, by using the WAN Optimization solution, application access will be faster. Meanwhile, SSL VPN is a solution for remote access.
Along with the growing trend of BYOD (Bring Your Own Device), we can work anytime and from anywhere. For employees or workers who usually work via mobile, they will access the company network using the remote access method. Using SSL VPN allows mobile workers to access company resources through mobile remote access applications and can do it safely. Because SSL VPN is made with access security features such as authentication, host checker and others.
Table of Contents
Sangfor Indonesia Partner
Enseval company has many branches which have challenges where it must be able to control and optimize every data owned by the company which is also added to require integrated security protection from the application surface to more technical stages in order to protect company data. With these various problems, the Enseval company, which is engaged in distribution and logistics, is realizing that it is starting to realize the importance of digital transformation that can support the effectiveness of Enseval’s company performance.
In addressing these challenges, a leading cloud and security solution provider company, Sangfor. As a partner, Sangfor Indonesia offers a very precise solution, namely by using NGAF and WAN Optimization. This solution also provides the best acceleration for the company’s wide area network.
A little explanation of Ngaf products that offer data protection or firewall solutions. NGAF or Next Gen Applications Firewall is a product breakthrough that is your first choice for protecting the security of your company data. Good for managing various types of cyber attacks which are of course very dangerous to your business.
And also the costs and time spent are also not small. So that with Sangfor NGAF, this can be resolved in which time and effort is spent in making data security more secure.
By managing various types of risks, NGAF provides various solutions and directions against these cyber attacks and also helps prevent these attacks on certain applications that are targeted from internal and external.
In the IT world we are familiar with the name of Ransomware. Ransomware is the fastest growing cyber threat today. When the national government and large companies including the Partner Sangfor Jakarta were once the main target of this Ransomware, many local governments and smaller organizations have become victims now. Until the cessation of operation in a few days to weeks unless exorbitant ransoms are paid. On average, the fine costs of this Ransomware start at US $ 100K / hour or 1 billion rupiah per hour.
Ransomware is a type of malware or hacking device that uses a certain sequence of steps called “Kill a chain” to infect and spread to various victims’ computers.
Jakarta’s Sangfor Partner Focuses on Cessation of Ransomware
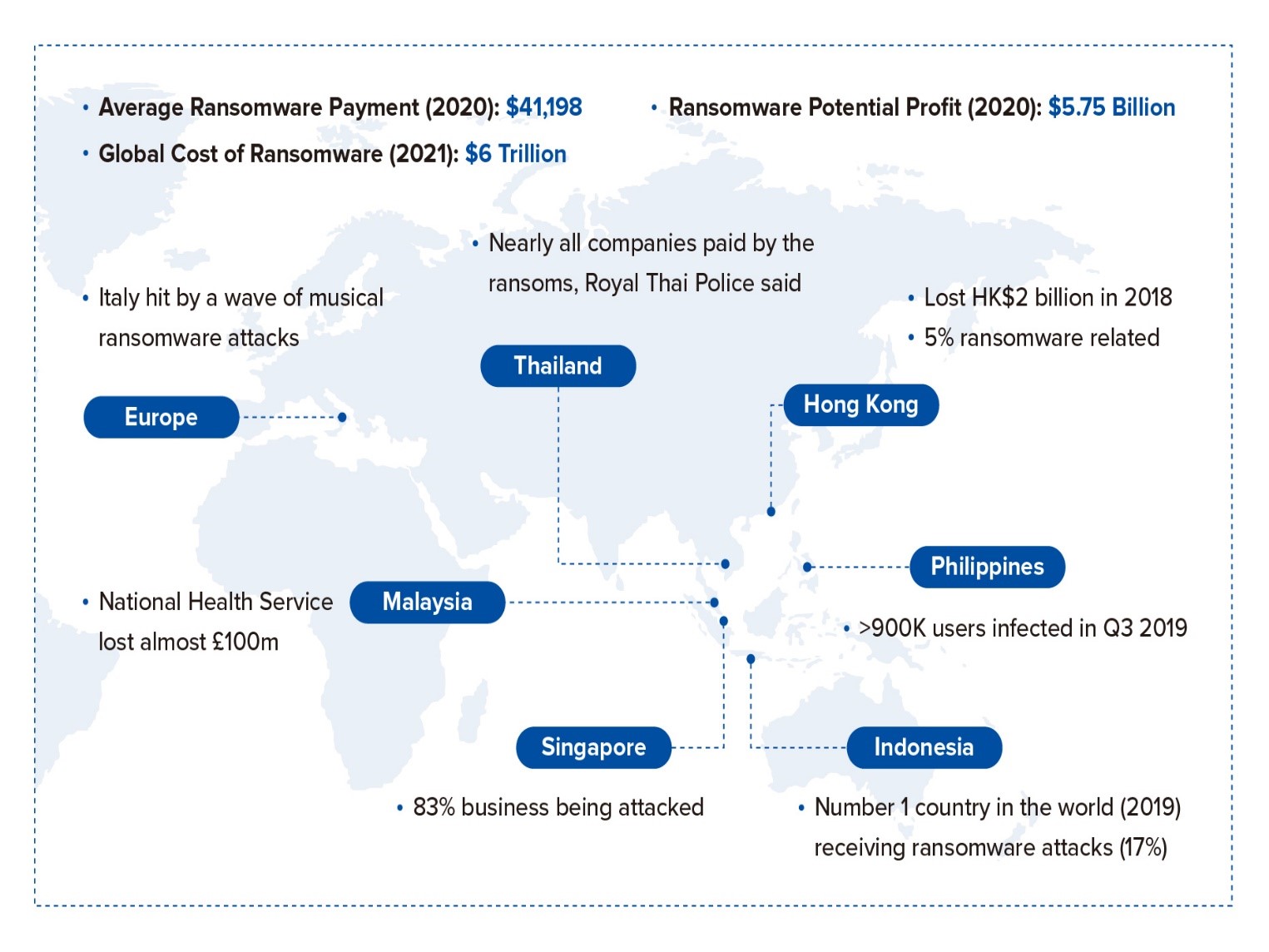 Traditional security point products alone have not stopped these steps effectively in this Kill Chain. A company may have protection with the latest generation firewall (NGFW), email gateway, and the latest generation of anti-virus / malware (NGAV) solutions, but WannaCry’s viruses or hacking devices prove ineffective by infecting 200,000 systems in 150 countries in just 4 days. Partner Sangfor Jakarta has outlined these steps to understand the reasons for the spread of Ransomware.
Traditional security point products alone have not stopped these steps effectively in this Kill Chain. A company may have protection with the latest generation firewall (NGFW), email gateway, and the latest generation of anti-virus / malware (NGAV) solutions, but WannaCry’s viruses or hacking devices prove ineffective by infecting 200,000 systems in 150 countries in just 4 days. Partner Sangfor Jakarta has outlined these steps to understand the reasons for the spread of Ransomware.
Analysis of Spread of Ransomware
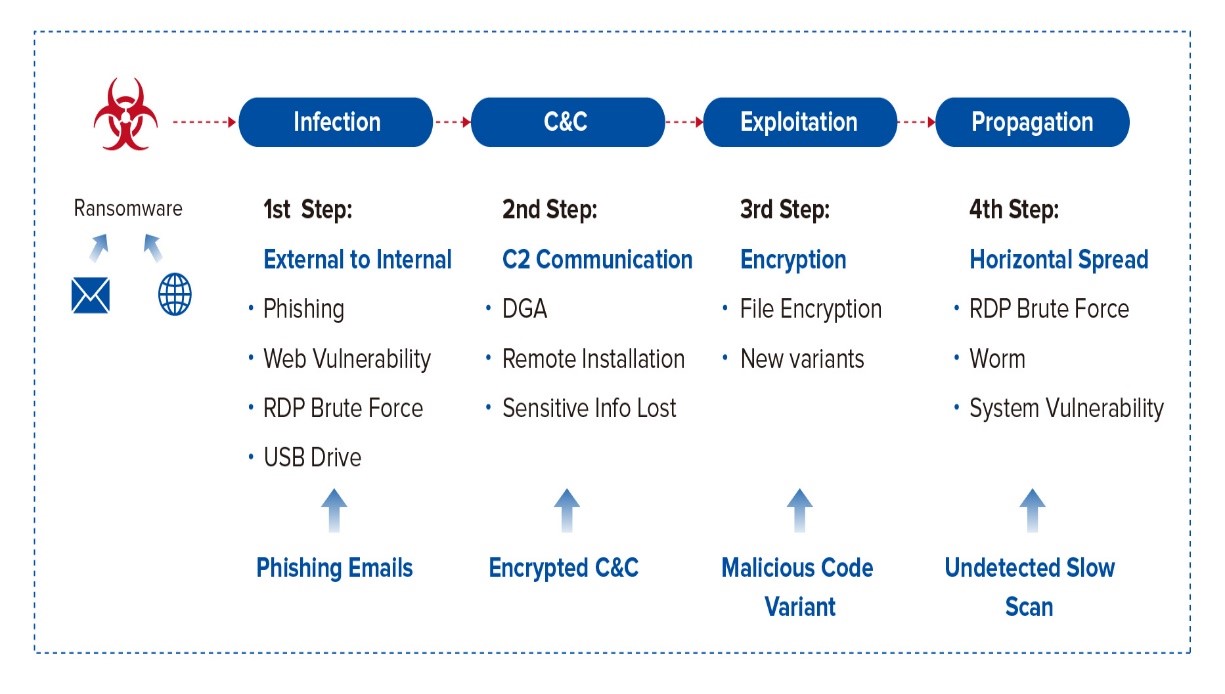
Infection
This infection occurs when an attachment or document is opened, or a link is clicked from a fake email. Same with clicking on a link on a dangerous website. This infection is a step that is usually fought by anti-virus / anti-malware products at this time. Anti-virus products scan files that are being downloaded or saved. Once found, the file is deleted or quarantined. The problem is that 3rd party testing shows that NGAV is 99.95% effective in detection. Effectiveness in this detection may seem quite high. However, AVTest receives more than 350 thousand new malware samples every day. Blocking 350 thousand new malware samples with 99.95% effective will potentially allow 1,750 samples. In other words, NGAF cannot block all viruses and may WILL escape detection. But NGAV doesn’t really function properly after installing malware.
C&C communication
NGAV cannot directly identify C&C malware communication. Firewalls can track communications to servers that are potentially exposed to C&C, but they cannot verify whether the communication is good or bad. Most NGAV and NGFW do not share information to identify that the infected file is communication with the C&C server.
Exploitation
The most difficult step to stop Ransomware is exploitation in which various files are encrypted. Ransomware does a great job of not only hiding the running system processes controlling encryption, but applications that start the process as well.
Propagation
The malware will spread to other vulnerable systems quickly, sometimes in just a few minutes. In many cases it is possible to isolate the system from the network to prevent it from spreading. However, infected systems may need to be operational for business requirements and cannot be isolated. The system will then look for other systems to infect the entire organization.
Holistic Solution
The Partner Sangfor Jakarta Security Solution for Ransomware provides a holistic solution to stop ransomware attacks in real-time. The solution is strong enough to block every step in the Kill Chain ransomware, but it is modular enough to suit any organization.
the need for internet in Indonesia has made many companies or individuals want to install this internet service either in offices or at home. Talking about the internet, it is not far from the name IT technology which many IT companies are developing in Indonesia such as Sangfor.
What is sangfor? Sangfor is a Multinational Company based in the city of Shenzen, the city of info technology in China. Sangfor Company in China has actually been established since last year. 2000 and developed together quite rapidly in China’s domestic market.
In addition, Sangfor also controls nearly 60% of the market share of intenret access management in China as well as getting many awards from Delloite, Fortune and also Frost plus Sullivan. In the Gartner Magic Quadran itself, the name Sangfor has appeared in the Niche Player area since 2011.
Trusted Partner
Partner Sangfor Indonesia offer solutions that cover three areas, namely Internet Access Management, WAN Optimization, and SSL VPN. Internet Access Management is a tool that is used to provide additional settings along with a high enough efficiency level for internet access activities. This solution is needed by almost all companies considering that almost all corporations already have access to the internet. With so many applications or platforms on the internet, regulation is too necessary so that internet access is used in accordance with company needs.
There is a WAN Optimization solution that is integrated with an increase in the performance of an application. Usually WAN Optimization is used when users in a branch access applications or servers in the data center via a WAN network. As for some components, including latency and bandwidth that are not large, generally give additional effects that access to applications is slow. But together with using the WAN Optimization solution, application access will be faster. Meanwhile, SSL VPN is a solution for remote access.
Partner of Sangfor Indonesia NetData
Along with the growing trend of BYOD (Bring Your Own Device), Partner Sangfor Indonesia are able to work anytime and come from anywhere. For employees or workers who usually work via mobile, they will be connected to the company network together with the remote access method. By using an SSL VPN, it is possible for mobile workers to connect company resources through a remote access mobile application to be able to do it together safely. Because this SSL VPN is made together with access security features such as authentication, host checker and others.
Sangfor Jakarta Partner
NGAF also provides more like the reporting requirements that are included in the NGAF box. So there is no need for additional boxes that have accurate and precise reporting to be able to determine policies to prevent data from leaving even though it is attacked from the internet or external side.
In the NGAF box there is also WAF security so this makes NGAF have very complete features such as WAF, APT, IPS, and a firewall that is very mature ready for use in large industries.
So that simple operation and maintenance (O&M) can save time to focus further on developing even more sophisticated company infrastructure. By minimizing cyber attacks, there will be less downtime and this greatly reduces choked up your business processes.
There are several reasons that reinforce that Sangfor is compared to other firewall products which are quite expensive. Because Sangfor has a built-in WAF already installed that can be used by NGAF users, reporting that has been included is directly in the Sangfor NGAF box without having to buy it separately. So that the security of your company data is guaranteed and is also directly supported by Sangfor directly.
Not only that, NGAF can also provide solutions for the rapid increase of your business. Partners of Sangfor Jakarta Enseval have also experienced firsthand the benefits of WAN Optimiser or WANO after using Sangfor products.
Julius Eka Wimardini, as IT Infrastructure Manager, Enseval, said that the Sangfor WAN Optimization solution provides many improvements to the company’s computing system. “After using Sangfor’s WAN Optimization, I felt a significant difference. Starting from the speed of opening applications compared to before using, to the main application which has become much more stable. “
The company itself previously used WAN Optimization solutions and immediately chose Sangfor because it saw the company’s background and clear experience. “Initially, we were looking for a one optimizer solution and found several brands like the one that exists today. We also don’t know what it’s like to use one optimizer. Then we tried one by one, until finally we got along and decided to use Sangfor products, ”said Julius.
As is well known, currently the condition of Indonesia’s infrastructure is not very good. For example, currently there are many unstable connections and frequent breakdowns which create problems for Enseval company.
The Oracle EBS application in every Enseval company previously ran very slowly and so was the video conferencing which was of such low quality that users complained. Directly, the local Sangfor team from Indonesia has reversed the situation by conducting tests on several branches of the Enseval company. Sangfor WAN Optimization manages to reduce more than 60% of WAN traffic and improve video conferencing quality.
Since 2017, all Enseval Yang branches in Indonesia have used Sangfor’s WAN Optimization solution. Another benefit that Enseval’s company feels is the company’s ROI (Return of Investment) which is better than in previous years.
Sangfor offers a variety of solutions at fairly competitive prices, which are automated, which makes it unnecessary for your company to spend a lot of money just to get these solutions. Therefore, for your company that needs the right solution to IT network problems, you can choose NGAF and WAN Optimization from partner Sangfor Jakarta at NetData.
Sangfor Technologies is a leading global vendor of IT infrastructure solutions, specializing in Network Security & Cloud Computing with a wide range of products & services including Next Generation Firewalls, End Spot Protection, Managed Detection and Response, World Access Management, Infrastructure Hyper-Converged, Virtual Infrastructure Desktop, WAN Optimization, SD-WAN and many others.
Sangfor takes business needs and customer user experience seriously, placing it at the heart of our company strategy. Creative and constant commitment to deliver scores for our customers helps them to pursue sustainable growth. Sangfor currently has 6,000+ employees with more than 60 branch offices around the world in attractive locations such as Malaysia, Thailand, Indonesia, Singapore, South Korea, Philippines, Vietnam, Myanmar, Pakistan, UAE, Italy.
Sangfor is very focused on data security. For many companies, data is something we generally consider safe and healthy, stored on computers and difficult to access. If you are working with data from your customers, storing sensitive information from your industry or even just storing your employee information on your company’s servers or cloud, then data protection must be one of your big priorities.
Here are some reasons why you should consider your data protected:
Copying the rules sign
Regardless of the variety of data that you store onsite or pass through your company’s servers, whether it’s payroll, information and other data from your customers or other material that could affect the day-to-day profession of your employees, maintaining data security must be the number one priority for which company instead. With the GDPR coming into effect with a usage date of May 25, keeping your data protected will be more than just evaluating courtesy – it will be a regulatory requirement.
Data is stored securely
The main reason to keep your data protected is to consider the security of any information you store. In the case of customers, considering their data to be kept as safe as possible is the minimum most people want for the company in which they invest their time or money. By keeping your customer and employee data safe, you can protect your business reputation and your company’s public opinion, earning you a brand you can trust with that information.
Data that isn’t stored securely is much easier to access from hackers and outside sources – something many businesses are discovering today because of out-of-date or out-of-date data protection. If you want to protect your business reputation, then data protection is very important.
Promoting safe work practices
Safe work practices are supported in all aspects of the business, from health and safety to employee welfare. This same concept should apply to your data, and by enforcing security when handling data, sensitive or otherwise, you have employees who know better how to best manage and store that information. Data is the backbone that makes up many customer-focused businesses, and shouldn’t be a second thought.
If you already understand how important it is to secure data, then you just trust Netdata who is a Partner Sangfor Jakarta. Netdata has indeed been trusted to handle various things related to data security by relying on Sangfor.
Sangfor aCloud is a new generation of cloud IT architecture. This is built on innovative hyper-convergence technology, with a complete IT infrastructure and O&M management and operations capabilities. It can bring key business applications such as core databases, ERP, financial systems, production systems. Being a partner of Sangfor Indonesia is one of the right things.
Unlike traditional cloud solutions, Sangfor Enterprise Cloud which is built on HCI is more simplified and flexible, allowing users to quickly build business-driven cloud computing data centers; no matter it’s a private, hybrid or industrial cloud. This provides users with a collection of automated IT, IT as a Service, and IT O&M resources, making it easier for key businesses to migrate to the cloud. This is the preferred solution for government users, organizations and companies.
Enterprise Cloud is Built on Hyper-Converged Infrastructure
Traditional cloud computing architecture seems complicated. Overall platform performance is limited by physical equipment. Management of each component cannot be unified. Security devices cannot effectively deal with security threats in the cloud data center. At the same time, fragmented operating and maintenance tools make O&M more complicated, and the agility of the entire data center cannot be achieved.
Whereas, Sangfor Enterprise Cloud is based on HCI. It only requires a general x86 server and switches hardware, using software-determined technology to achieve the full collection of resources from computing, storage, networking and security. It can replace traditional complex cloud infrastructure to achieve minimalist cloud architecture. Not interested in becoming a partner of Sangfor Indonesia?
Application Key Migrate to Cloud
Due to the lack of a complete security system and guaranteed reliability for traditional cloud computing architectures, critical applications that migrate to the cloud are quite difficult. With the advantages of converging technology, partner of Sangfor Indonesia have made special optimizations for high network stability, performance and security requirements for critical applications. Users can use database clusters such as Oracle RAC and major applications such as ERP to Sangfor Enterprise Cloud, make all applications nimble and resilient, and let better IT drive business transformation.
Therefore, check now the Netdata website at nds.id which is a Partner Sangfor Jakarta. Guaranteed you can get a variety of very attractive offers!
![]()


