Having the assets of a computer network security must be interspersed with securing the computer network. Network security is very important because keeping a computer system awake without any interference from within or from outside will make the network run more smoothly. If you are sure of the network security you have, it’s time to do the testing, and the test is called penetration testing.
Before reading further, for those of you who want to know more about Netdata, you can contact us directly via the link below.
What is called penetration testing? And is penetration testing important for computer network security?
Table of Contents
Understanding About Computer Networks
A computer network is a collection of computing devices connected to each other for the purpose of sharing information and resources among various users.
Each device in the network is called a node which is connected to other nodes via wired or wireless media.
Computer Network Security
This computer network security consists of the concept. There are 3 important concepts in network security, including:
- Confidentiality
Confidentiality is equivalent to privacy. Privacy is designed to contain sensitive information and ensure that the right people have access. Sometimes protecting the confidentiality of knowledge can involve special training for those who understand the document.
2. Integrity
Integrity involves protecting the consistency, accuracy and trustworthiness of data. Data cannot be modified, and several steps must be confiscated to ensure that knowledge cannot be altered by unauthorized persons.
3. Availability
Availability is the best plan that can be ensured in maintaining all hardware, carry out repairs to hardware as soon as possible when needed. It also includes being able to maintain the operating system environment.
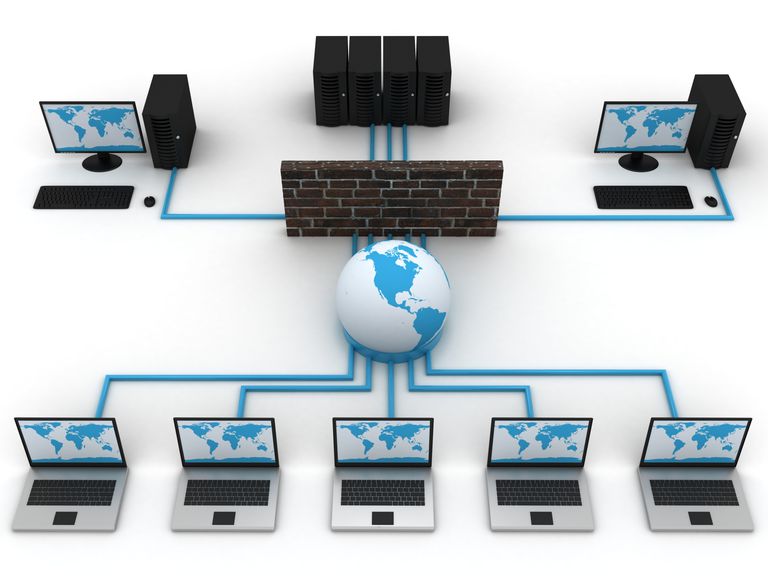
Type of Network Security Device
After knowing the important concepts of network security, network security can be further dissected, namely based on the type of network security device. These types of devices include:
- Active Devices
Some examples of this Network Security model include Firewalls, antivirus scanning tools, and content filtering tools, which block excessive traffic.
- Passive Devices
These tools identify and report unwanted traffic, such as, for example, intrusion detection appliances.
- Preventative Devices
This device scans the network and identifies potential security cases. For example, penetration testing devices and vulnerability assessment appliances.
- Unified Threat Management (UTM)
This device serves as an all-in-one security device. Where examples include firewalls, content filtering, website caching, and others.
Is it Important to Secure a Computer Network?
If this question arises in the minds of many people and maybe in yours, then the answer is “Yes, securing a computer network is very important!”
Computer network security keeps sensitive data safe from cyber attacks and ensures that the network is usable and trustworthy. Network security management may involve a variety of security tools, both hardware and software.
Securing Computer Networks
To be able to secure computer networks, there are several things that need to be considered thoroughly, namely how to prevent computer networks from hacking and data theft. The method is as follows:
Enable Network Encryption
Enable WPA2 on the Wi-Fi router. This is the current standard for encrypting hotspot networks. WPA2 can be said to be an encryption system that is compatible with various network systems.
Update Router Software Periodically
Updating router software regularly is very important, these updates usually bring the latest network security from the developer. Thus, various bugs or gaps for hacking will be fixed by the developer.
Using Firewalls
The last is to activate and use the firewall. The firewall referred to here is for your router whose role is to provide an additional layer of security on the router. Most routers have actually been added with Firewalls and can be updated regularly to strengthen security. This firewall can block threats that enter the network automatically so you don’t need to keep an eye on it.
Penetration Testing
Network security by testing is an interesting thing. For example, when making fruit ice, after mixing several ingredients, you will try whether it is sweet or not before you drink it completely. Roughly according to the simplest understanding of penetration testing is like that, namely testing computer networks about whether the security system is safe or not.
Computer network security can be revised if, for example, after penetration testing it turns out that there is a security system that is lacking.
Definition of Penetration Testing
Penetration testing or pen testing is an attempt to evaluate the security of IT infrastructure by trying to exploit vulnerabilities safely. These vulnerabilities may be in operating system, service and application flaws, improper configuration, or risky end-user behavior. Such assessments are also useful in validating the efficacy of defense mechanisms, as well as end user compliance with security policies.
Penetration testing is typically performed using manual or automated technology to systematically compromise servers, endpoints, web applications, wireless networks, network devices, mobile devices, and other potential points of exposure.
Penetration Testing Methods
In doing penetration testing, there are several methods that can be done, namely black box testing, gray box testing, and white box testing. Everyone has their own way.
The following is an explanation of the penetration testing method.
Black Box Testing
Penetration testing using the black box testing method is a test that only considers the external behavior of the system; the internal workings of the software are not taken into account. It is done by the examiner directly.
This method is used in System Testing or Acceptance Testing. Black box testing is the least time consuming than the other methods. It is also known as data driven testing, functional testing and closed box testing.
Gray Box Testing
Between black box testing and white box testing, there is a test in the middle, namely gray box testing. This is a method that can be used to debug software and evaluate vulnerabilities. In this method, the tester has limited knowledge about the workings of the components being tested. This is in contrast to black box testing, where the tester has no internal knowledge, and white box testing, where the tester has full internal knowledge.
It can be implemented as an unbiased and unobtrusive form of penetration testing. In this test, the tester usually knows what the internal components of the application are, but does not know how these components interact. This ensures that tests reflect the experiences of attackers and potential users.
White Box Testing
The last one is white box testing. Is a method used to test software by considering its internal functions. This is done by software developers. This method is used in Unit Testing or Integration Testing. This is the most time consuming.
White box testing is testing software logic. It is also known as clear box testing, code based testing, structural testing and transparent testing. White Box Test is very suitable for testing algorithms.
Penetration Testing Is Important For Computer Networks
Doing penetration testing on a computer network has many advantages and is indeed very important. Because of its importance, maybe computer networks ranging from small to large ones can really do this because data theft from irresponsible parties does not discriminate.
The following is the importance of penetration testing for computer networks:
- Preparation For Attack
The main reason penetration testing is so important for organizational security is because it helps personnel learn how to deal with all kinds of intrusions from malicious entities. This test serves as a way to check whether an organization’s security policies are truly effective.
2. Risk identification
Penetration testing also offers insight into which channels in an organization or application are most at risk and thus what types of new security tools to invest in or protocols to follow.
3. Reduce the Number of Errors
Penetration testing reports can also help developers make fewer mistakes. When developers understand exactly how malicious entities launch attacks on applications, operating systems, or other software they help develop, they will become more dedicated to learning more about security and less likely to make similar mistakes in the future.
NetData is a company that provides the highest quality technology-based services, if you are interested in us you can contact us directly via this link or via our contact form here.
![]()