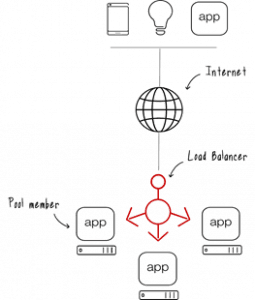
HP Load Balancer
HP Load balancer is a device that acts as a reverse proxy and distributes network or application traffic across a number of servers. Load balancers are used to increase the capacity (concurrent users) and reliability of the application. They improve overall application performance by reducing the load on the server associated with managing and maintaining application and network sessions, as well as by performing application-specific tasks.

DESCRIPTION
HP Load Balancer
HP Load balancer – Most commonly, the term load balancing refers to distributing incoming HTTP requests across Web servers in server farms, to avoid overloading one server. Since load balancers distribute requests based on the actual load across each server, it is great for ensuring availability and withstanding denial of service attacks.
Accepted by both types of load balancer and distributed to specific servers based on a configured algorithm. Some of the industry standard algorithms are:
- Round robin
- Weighted round robin
- Least connections
- Least response time

Layer 7 load balancers can further distribute requests based on application-specific data such as HTTP headers, cookies, or data in the application message itself, such as specific parameter values.
Load balancers ensure reliability and availability by monitoring application “health” and only sending requests to servers and applications that can respond in a timely manner.
Load Balancer from F5 HP Indonesia has the perfect solution for the network load balancer needs you need with guaranteed reliability.
The BIG-IP platform is a smart evolution of Application Delivery Controller (ADC) technology. The solutions built on this platform are load balancers plus full proxies that provide visibility into, and the power to control, all traffic passing through your network.
For business growth
Organizations can dynamically add more servers to respond to an increasing number of users or anticipate requests
Integrated, unified secure user access to ensure the right people have the right access to the right applications – anytime, anywhere.
Gives you protection for your applications in Layers 3 and 4 against the most aggressive volumetric DDoS attacks.
Gives you the flexibility to deploy web application firewall services closer to your application to be protected wherever you are.
Allows you to create and manage policies to manage web access, as well as identify and block web-borne threats.